Labour has been hit by two co-ordinated cyber-attacks from users reportedly based in Brazil and Russia. The party has said no data breach occurred, meaning that no personal information was taken by the attackers.
The type of cyber-attack Labour experienced is called a DDoS – a distributed denial-of-service. This kind of attack is designed to stop a website from working by flooding it with a lot of requests from different areas. The aim is usually not to steal data.
The “visitors” – not actual people typing “Labour.org.uk” into their browser but often software designed to imitate people – visit a particular website at the exact same time. This causes it to slow down and, in some cases, stop working completely.
How does this work? Put simply, websites are a series of files hosted all over the world. These files are stored on computers called servers. When you type “google.com” into your browser, your computer – which has a unique identifier called an IP address – requests the files from the server that hosts the website.
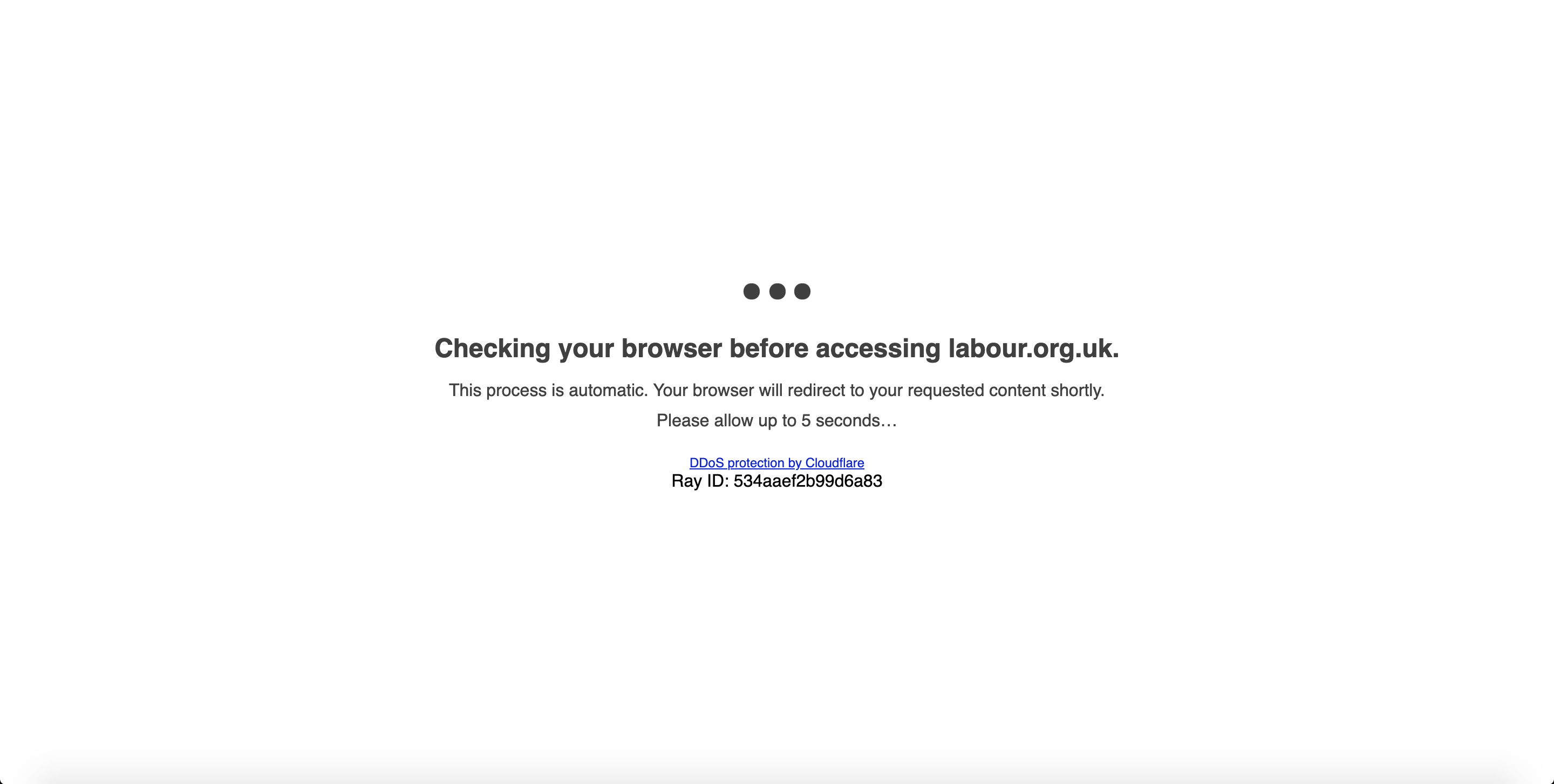
Many organisations like Labour use a service called Cloudflare to store their websites. You’ve probably heard of Cloudflare because 20 million websites use it. It stores copies of a website on multiple servers across the globe to make your website load quickly wherever you are.
Although we think of the internet as being “in the air” (particularly because people have taken to calling everything “the Cloud”), most information travels by physical cables from a server to your computer or phone, so your proximity to the information actually makes a difference to how quickly it loads. You might notice this is you visit websites ending in “.com.au” and “.co.uk” – the former may load more slowly than the latter.
Because servers are physical computers responding to requests from computers, they slow down when lots is asked of them, just like your laptop does when you’ve got lots of tabs open, for example, and can also only handle a certain amount of requests at a time. This is what a DDoS attack relies on.
Attackers from a variety of locations co-ordinate huge amounts of traffic to the same website at the same time, which causes the servers attempting to respond to those requests to either shut down or stop working. Cloudflare, the system Labour uses, has particular protections in place to ensure their servers and the websites they serve can’t be downed by a DDoS.
What can Labour do to protect itself from these attacks? Unfortunately, there isn’t much more they can do – Cloudflare provides some of the best protection against DDoS attacks providers have to offer, keeping the sites active while stopping any real damage being done.
Some of this is invisible: your computer might have loaded the website from Dublin rather than London. Some of this is visible: if you’d have visited Labour’s sites at any time during the attack, you might have seen an image similar to the one below. This was to detect whether or not you were a legitimate visitor. During this time, Cloudflare might also have increased the capacity of their servers to provide support for the traffic, which would be useful if the increase in traffic was legitimate.
How do we know where the attackers came from? The truth is we don’t, really, but we do know their purported locations are Russia and Brazil. This is based on the location of the IP addresses used to carry out the attacks. Although you or I might not even know ours (hint: google “what is my IP address”), others can mask theirs to hide their identity and location. Whoever has carried out these attacks has done just that, to make it at least look as if they’re attacking Labour from these countries.
That is not to say that the attacks are coming from somewhere other than Russia and Brazil. While we may not know the exact identities of the attackers, it is possible that the servers or computers carrying out the attacks are located in those areas. And for some attackers, revealing their location is part of the appeal.



More from LabourList
Letters to the Editor – week ending 24 May 2026
‘Young Labour elections give radical realists a path to power’
‘Labour has work to do to regain the trust of Prospect members’